network intrusion protection system (NIPS)
What is a network intrusion protection system (NIPS)?
A network intrusion protection system (NIPS) is an umbrella term for a combination of hardware and software systems that protect computer networks from unauthorized access and malicious activity. A NIPS helps organizations detect and respond to potential threats in real time, maintaining the integrity and confidentiality of data.
These systems are placed inline with the flow of network traffic, where they examine network packets, protocols and patterns to identify suspicious behavior, such as unauthorized access attempts, malware infections and data breaches. A NIPS detects problems and alerts administrators to potential issues. In doing so, it plays a crucial role in minimizing the impact of cyber attacks and fortifying network defenses.
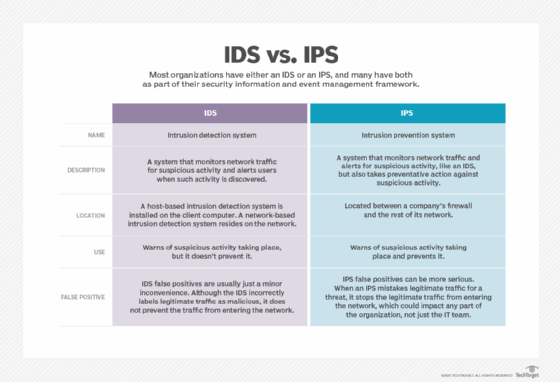
NIPS hardware often consists of a dedicated network intrusion detection system (NIDS) device, an intrusion prevention system (IPS) or something that functions as a combination of the two, such as an intrusion prevention and detection system. A NIDS detects intrusions, while an IPS proactively stops attacks by following preestablished rules to prevent them.
How does a NIPS work?
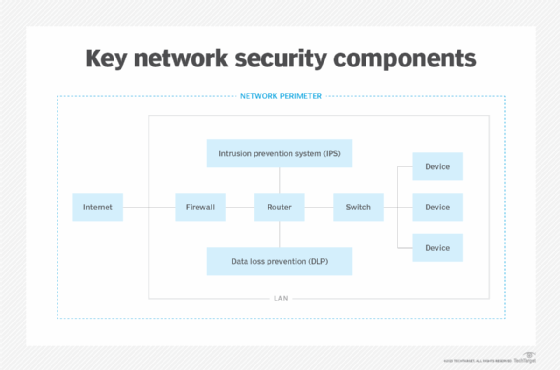
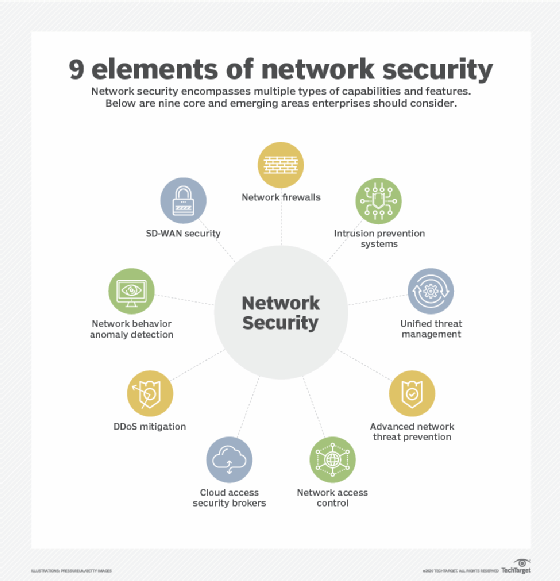
The software components of a NIPS consist of firewall, sniffer, antimalware and antivirus tools, along with dashboards and data visualization tools. These components work together to continually monitor an organization's computer networks and network perimeters for abnormal traffic patterns and malicious traffic.
Once an anomaly is discovered, the NIPS alerts system administrators to significant events and might even automatically stop potential intrusions. A NIPS uses the following techniques for screening data for anomalies:
- Signature-based detection. The NIPS scans and analyzes data for patterns or signatures of known malware. It regularly updates its database of known signatures and rules to maximize its effectiveness.
- Anomaly-based detection. The NIPS monitors for suspicious or unfamiliar network traffic patterns by using network behavior analysis to sample network activity and regularly compare those samples to a baseline standard. This technique also requires consistent updates to the database of rules and patterns, though newer systems are using artificial intelligence and machine learning to streamline these processes.
- Policy-based detection. Network administrators set specific network security policies and create rules tied to them. Network traffic is monitored for adherence to those policies and rules, and traffic patterns that go against them trigger a response from the system.
A NIPS might use a honeypot or decoy system to attract attackers. Once it detects an anomaly, it takes several actions in quick succession, such as the following:
- Drops suspicious packets.
- Blocks IP addresses from suspicious traffic.
- Quarantines suspicious code for further analysis.
- Notifies network security administrators.
- Generates event logs.
- Revises rules for firewalls and other devices.
- Resets all network connections.
A NIPS is different from a host-based intrusion prevention system, or HIPS, which gets installed at an endpoint and only monitors inbound and outbound traffic for that device. It also differs from a wireless intrusion prevention system, or WIPS, which monitors wireless networks for intrusions.
Why is a NIPS important?
Spyware, distributed-denial-of-service (DDOS) attacks, phishing, viruses, ransomware and other malware attacks continue to grow in frequency. Intrusion protection systems are part of the layered cybersecurity systems networks need.
Some form of a NIPS is vital for any computer network that's at risk of access by unauthorized persons. Computers holding sensitive data always require protection against advanced threats, but even seemingly insignificant networks can be hijacked for use in malware attacks.
In addition to the attack detection and prevention, a NIPS provides documentation demonstrating compliance with various regulations. Organizations need such documentation when conducting security audits.
Benefits and challenges of a NIPS
NIPS technology provides organizations with the following advantages:
- Reduces the likelihood of cyber attacks and the issues that come with them.
- Increases threat protection and network visibility.
- Facilitates anomaly analysis.
- Automates network activity monitoring.
- Notifies administrators about any threats or anomalies.
- Makes information readily available to admins.
However, these systems have some challenges, such as the following:
- These systems must be regularly reviewed and updated to ensure their rules and analytical tools remain up to date.
- Insufficient network bandwidth and capacity can result in slower applications while the NIPS operates.
- They can generate false positives that might unnecessarily deny service to users.
IDS vs. IPS: Which is better?
An IDS identifies and highlights suspicious activity and reports it to network administrators. The admins then must address the anomaly.
An IPS both detects anomalies and takes action to block them from causing harm to networks and systems. This makes an IPS -- and, by extension, a NIPS -- the preferred approach.
What's the difference between a firewall and a NIPS?
Firewalls and network intrusion protection systems are both key components of network security systems. Nevertheless, there are distinct differences between a NIPS and firewall. They serve different purposes and complement each other in comprehensive network security strategies, such as unified threat management and next-generation firewall systems.
Firewall
Firewalls act as the first line of defense, providing a barrier between an organization's internal network and the external internet. They examine incoming and outgoing network traffic based on predefined rules and policies. They also monitor and control traffic flow, allowing and blocking access based on specified criteria.
Firewalls can be implemented at various levels, such as on networks, applications and even individual devices. They're designed to protect against unauthorized access, DDOS attacks, malware and other threats by filtering and inspecting packets. By analyzing packet headers and content, firewalls can enforce security policies and prevent malicious activities from entering or leaving a network.
Network intrusion protection system
A NIPS is a more advanced security approach to detecting and preventing network intrusions that goes beyond the capabilities of a firewall. A NIPS focuses on detecting and preventing network intrusions in real time. It uses techniques like signature detection, anomaly detection and behavior analysis detection methods to identify malicious activities within the network.
A NIPS monitors network traffic continuously, looking for patterns or anomalies that may indicate an attack or unauthorized access. When a potential threat is detected, the system takes immediate action to block the IP addresses of questionable traffic or otherwise mitigate the attack, preventing further damage.
Learn more about incident response to effectively detect, manage and prevent cyber attacks in the enterprise.
