What is Wi-Fi Piggybacking?
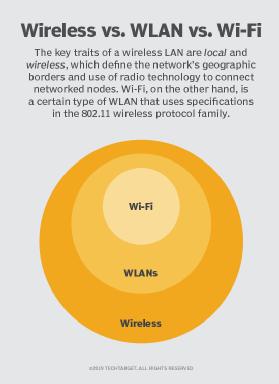
Piggybacking, in the context of Wi-Fi, is the use of a wireless connection to gain access to the internet without proper authority. Piggybacking is also sometimes referred to as Wi-Fi squatting and tailgating.
What is the purpose of piggybacking?
The purpose of piggybacking is simply to gain free network access.
Often this isn't done with malicious intent, but it is still considered theft because the user is taking advantage of a service that they have not paid for or don't have the legal right to use.
A network that is vulnerable to piggybacking for network access is equally vulnerable when the purpose is a data breach, dissemination of viruses or some other illicit activity.
How does piggybacking work?
Piggybacking worked in the past because all one would have to do was take advantage of the fact that most Wi-Fi networks were not encrypted. This means that anyone within range of the signal could access the network without having to enter a password.
To access an unsecured wireless network, all you had to do was to get into the range of a Wi-Fi hotspot's signal and select your chosen network from the options presented.
Today most Wi-Fi networks are encrypted with passwords, which makes piggybacking much more difficult. It is still possible for someone to access a network if they have the password or if they can crack the encryption.
What are the consequences of piggybacking?
As stated previously, piggybacking is illegal. People have been fined for accessing hotspots from outside businesses, such as coffee shops, that provide free Wi-Fi for customers' use.
In some cases, people have been arrested for accessing Wi-Fi networks without permission.
Piggybacking can also lead to slower internet speeds for everyone on the network, as well as decreased security.
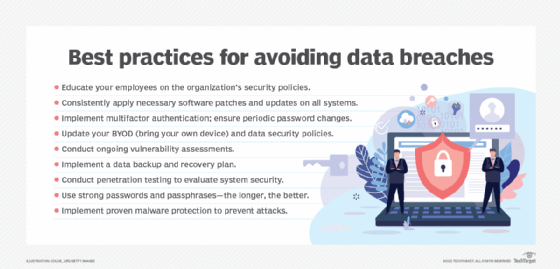
How can you prevent piggybacking?
The best way to prevent piggybacking is to make sure that the Wi-Fi network and router are properly secured with a strong password.
Also, keep an eye out for people loitering outside of businesses or other places where Wi-Fi is accessible. If users see someone hanging around who doesn't seem to belong, let a manager know.
People should also use a strong password for their Wi-Fi network and make sure that it is not easily guessed. A strong password should be at least eight characters long and include a mix of letters, numbers and special characters.
You can also consider using a virtual private network (VPN) to encrypt your internet traffic and keep your data safe from prying eyes when using public Wi-Fi hotspots that are open to the public.
See also: watering hole attack, dumpster diving, shoulder surfing, social engineering, ransomware