digital profiling
What is digital profiling?
Digital profiling is the process of gathering and analyzing information about an individual that exists online. A digital profile can include information about personal characteristics, behaviors, affiliations, connections and interactions. Digital profiling is used in marketing, enterprise security, criminal justice and recruitment, among other areas.
Enterprise security applications for digital profiling
In enterprise security, digital profiling is used to identify suspect employees and protect the organization from an insider threat. An employee may be singled out because of suspicious behavior. To determine whether they pose a risk to the company, their online behavior may be scrutinized and a digital profile assembled.
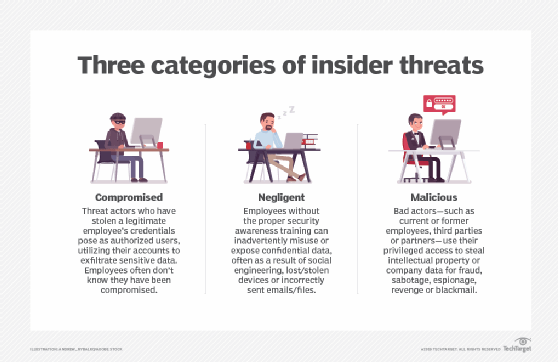
In a low-profile case, information is typically gathered through corporate email, logs, and social media content, connections and posts. In recent years, advanced analytics and machine learning algorithms have enhanced the ability to detect insider threats by analyzing large volumes of data for patterns and anomalies.
In a more high-profile case, investigators might employ surveillance technologies for a more complex profile of the individual.
Criminal justice applications for digital profiling
In criminal justice, digital profiling is used to identify suspected criminals and people of interest. Law enforcement officials work with forensic psychologists and combine a digital profile with other information that is known about a given individual.
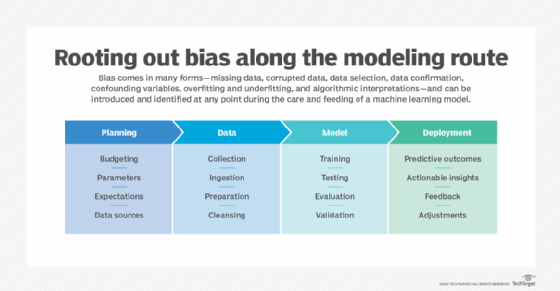
The integration of digital profiling with predictive policing techniques has further enabled law enforcement agencies to anticipate and prevent criminal activities more effectively. However, these techniques aren't perfect, as bias can creep into the modeling algorithms used in modern digital profiling.
HR applications for digital profiling
In human resources (HR) management, recruiters and hiring managers use digital profiling to find and assess potential employees. In combination with traditional employee vetting using resumes and interviews, potential hires are evaluated based on their digital profiles, or digital footprints.
Recruiters may use social media sites for professionals, like LinkedIn, where users can create profiles that are appealing to potential employers. Social media activity can add to a candidate's digital profile both positively and negatively, as social media analytics become a larger part of recruiting efforts by employers.
Recent trends show an increasing reliance on artificial intelligence (AI)-powered tools to automate the screening process, making digital profiles even more critical in the hiring process.

Marketing applications for digital profiling
Digital profiling is also extensively used in marketing to tailor advertising and personalized content to specific audiences. By analyzing online behavior preferences and demographics through web analytics, marketers can create detailed customer profiles and deliver targeted advertisements that are more likely to resonate with potential customers. This practice helps optimize conversion rates and customer engagement.
Privacy concerns and ethical considerations for digital profiling
While digital profiling offers many benefits, it also raises significant privacy and ethical concerns. The collection and analysis of personal data without explicit consent can lead to privacy infringements.
Organizations must navigate regulatory requirements, such as the General Data Protection Regulation, and ensure that their profiling practices are transparent and respectful of individual privacy rights. In addition, organizations should consider avoiding biases in profiling algorithms and ensuring that data is used fairly and responsibly.
Businesses use AI in many ways but not without privacy risks anymore. An AI ethics committee can help mitigate these problems, however. Learn why you need an AI ethics committee. Also, read about common social media privacy issues and data privacy challenges and how to fix them.
