What is BASIC (Beginner's All-purpose Symbolic Instruction Code)?
BASIC, short for Beginner's All-purpose Symbolic Instruction Code, is an early programming language that was designed to help non-technical users and students solve easy problems with a computer. With its simple commands and user-friendly syntax, BASIC remains one of the simplest languages developed for programming in the computer age.
Advantages of BASIC
One of the key advantages of BASIC is that it can be learned quickly. It removes the need for users to understand low-level code constructs or how the underlying computer hardware works. Furthermore, it is an interpreted language with individual lines of code executed in real time. For all these reasons, BASIC is easy to learn and use, even by non-technical users with little programming experience or a mathematical background.
In addition to ease of use, BASIC is a highly versatile language. It is also expandable, generates robust code and is interactive, making it suitable for developing a wide variety of applications -- both simple and complex. BASIC is also a good choice for teaching programming concepts to students since it is easy to learn. Another advantage of BASIC is that it is independent of both hardware and operating systems (OSes, which explains its rise in popularity among hardware developers for many years after its initial release.
BASIC's concepts and syntax have influenced many modern programming languages, including Java, Python, Pascal and Scala. Additionally, BASIC remains the foundation of Microsoft Visual Basic, an object-oriented programming language that remains a popular choice for programmers looking to build type-safe .NET apps, system applications, back-end programs and even chatbots.
History of BASIC
In 1963, John Kemeny and Thomas Kurtz, two mathematicians and computer scientists at Dartmouth College in the U.S., developed BASIC as a general-purpose, high-level, user-friendly programming language. Their goal was to help Dartmouth students to easily write simple programs for the college's large-scale time-sharing system, known as the Dartmouth Time-Sharing System, or DTSS. BASIC enabled these students to solve simple problems with DTSS without having to write complex programs. They could also avoid programming in the difficult, complicated languages of that era like Assembly and Fortran that required advanced programming knowledge or expertise -- which few students had.
Even though it was originally designed as an interactive mainframe timesharing language, the use of BASIC exploded for personal computers and microcomputers very quickly after its release by Kemeny and Kurtz. It became popular with hardware developers because it worked with a one-instruction-per-line format, used Boolean instructions like IF and THEN, and because it had a small footprint.
Apple and IBM were among the earliest companies to adopt BASIC in their computing hardware. In 1975, Microsoft developed Altair BASIC, a BASIC interpreter for the Altair 8800 personal computer. This interpreted version of BASIC was interactive and simplified debugging. In the early 1980s, on IBM's first family computer, the PCJr -- pronounced PC Junior -- a BASIC cartridge was a popular add-on. In addition to standard BASIC commands, the computer also supported new BASIC commands to allow users to use its audio and video features.
Over time, other systems started supporting BASIC, including the Commodore 64 from the now-defunct Commodore Business Machines and the Apple II. As the availability of BASIC expanded, so did its use, which helped accelerate the development of new kinds of software programs and games. Consequently, BASIC played an important role in expanding the fields of computer programming and software development. It also made software education more accessible to a greater number of interested learners.
BASIC today
BASIC is used in many business applications and is still considered a valid choice as a programming language for some purposes. Although its popularity has waned over the years with the emergence of newer, more robust languages, BASIC continues to be used because it can be learned quickly, its statements are easy to read by other programmers and support is available on most operating systems. Furthermore, because of its simplicity, BASIC is frequently used to teach the introductory concepts of programming with a working language.
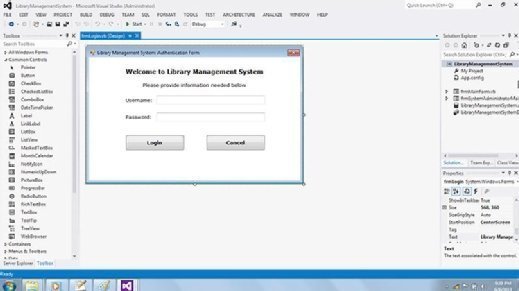
Microsoft's Visual Basic adds object-oriented features and a graphical user interfaceto the standard BASIC, allowing programmers to easily drag and drop elements like buttons or text instead of having to design those components from scratch. BASIC's documentation has been translated into many languages, making it accessible and available to a large number of learners and professional programmers. It often comes with sound and graphics support.
BASIC versions and products
BASIC is a family of programming languages rather than one isolated language.
Between 1964 and 1970, BASIC's inventors Kemeny and Kurtz released multiple versions of the language, including the simply named BASIC the Sixth. In the 1970s, many individuals and organizations further developed BASIC. Gordon Eubanks -- who went on to become the CEO and president of Symantec (now part of Gen Digital Inc.) -- developed BASIC-E and CBASIC.
In BASIC-E, instructions are first transformed into intermediate code and then converted into machine-readable code. The language was part of Eubanks' master's degree thesis and was based on his thesis advisor Gary Kildall's CP/M operating system. BASIC-E was never patented. On the other hand, Eubanks did patent CBASIC, which he wrote for IMS Associates, Inc. for the company's 8080 microcomputer. CBASIC included the binary-coded decimal system, where a digit is represented by a fixed number of bits. With BCD, CBASIC eliminated the rounding errors that were prevalent in other versions of BASIC like MBASIC (Microsoft BASIC).
MBASIC is Microsoft's BASIC implementation for the CP/M OS. An improvement over Altair BASIC, which was Microsoft's first BASIC implementation and one of the first BASIC versions that could run on a very small amount of RAM, MBASIC includes hardware-neutral functions. This advantage notwithstanding, MBASIC also had one disadvantage -- rounding errors. Eubanks' CBASIC eliminated this problem.
ANSI (American National Standards Institute) also created two versions of BASIC: Minimal BASIC and Standard BASIC. The organization released the specification for Minimal BASIC in 1978 and Standard BASIC in 1987. Prior to this, Bob Albrecht and Dennis Allison created TinyBASIC that, like Altair BASIC, could run on a small amount of RAM -- only 2 K. Other companies that created their own version of BASIC include Radio Shack, Atari, Apple and Texas Instruments.
QBASIC is another popular version of BASIC. Like other versions, QBASIC is easy to learn and therefore suitable for beginner programmers. It is based on the DOS OS but can also be executed on Windows systems. It includes a built-in interpreter that immediately executes the source code within QBASIC's integrated development environment, as well as a debugger and several prewritten example programs.
As the IT environment evolves, it has become more competitive. Developers can enhance their skill set and career potential by learning new programming languages. Also, compare six popular languages head to head.
