What is Amazon? Definition and company history of Amazon.com
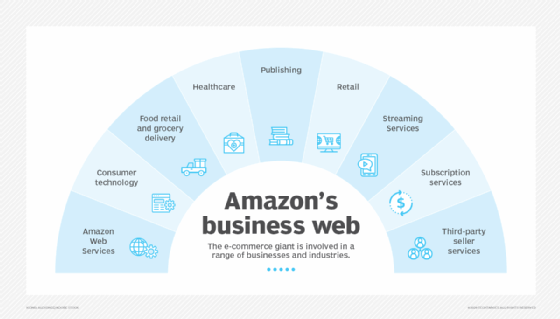
Amazon (Amazon.com) is the world's largest online retailer and one of the largest providers of cloud services. As of 2025, it is considered a giant in both e-commerce and cloud computing.
Headquartered in Seattle, Amazon has individual websites, software development centers, customer service centers, data centers and fulfillment centers around the world. The company was founded by Jeff Bezos in 1994; he remained its CEO and president until 2021. As of 2025, he remains Amazon's executive chair and one of its largest individual shareholders.
What is Amazon known for?
Originally an online bookselling company, Amazon has morphed into an internet-based business enterprise that provides cloud computing, digital streaming and AI services, in addition to an e-commerce platform.
The platform operates in more than 20 countries worldwide. These active Amazon marketplaces serve hundreds of millions of customers annually, offering a monumental product range and inventory. They allow consumers to buy just about anything, including clothing, beauty supplies, gourmet food, jewelry, books, movies, electronics, pet supplies, furniture, toys, garden supplies and household goods.
In more recent years, Amazon gained prominence as a cloud service provider. The company launched Amazon Web Services (AWS) in 2006 to provide cloud computing services like compute, storage, databases and networking to organizations. Through these offerings, along with emerging technologies like AI, data lakes, analytics and IoT, Amazon aims to help companies and government agencies lower costs and enhance their agility and competitiveness.
Apart from its main offerings -- e-commerce platform and 200+ cloud services -- Amazon is known for many of its other products, some of which are very popular. These include Twitch (a live streaming service), Kindle (e-book reader), Fire (tablets and TVs) and Alexa (smart speakers). The company is highly regarded for its ability to innovate and for being highly customer-centric.
History and timeline of Amazon
Amazon has come a long way since it was founded by Jeff Bezos in his garage in Bellevue, Wash., on July 5, 1994.
The following is a brief history and timeline of events that led to Amazon's evolution from its humble beginnings to a multinational business empire.
The 1990s
Amazon officially opened for business as an online bookseller on July 16, 1995, just one year after Bezos founded the company in his garage. For a few years, he shipped books to all 50 U.S. states and many other countries.
Originally, Bezos incorporated the company's name as Cadabra, but later changed it to Amazon. He is said to have browsed a dictionary for a word beginning with A for the value of alphabetic placement. He ultimately decided on the name Amazon because it was exotic and different, and as a reference to his plan for the company's size to reflect the vastness of the Amazon River, one of the largest rivers in the world.
Throughout 1995 and the first two quarters of 1996, Amazon was a loss-making company. However, in quarters three and four, its revenue rose and its losses fell. The company's losses continued to decrease over the next few years.
In the second half of the 1990s, Amazon achieved several milestones. It launched an affiliate program to increase its reach in 1996 and opened its first remote distribution center in 1997. In 1998, Amazon made its first acquisition -- Internet Movie Database (IMDb) -- a website that provides information about movies and TV shows and is now used by millions of people worldwide.
The early 2000s
In October 2000, Amazon launched its first overseas operations in Japan. The Japanese Amazon marketplace remains accessible at www.amazon.co.jp.
In the last quarter of 2001, Amazon turned a profit for the first time in its history. Then, 2003 became its first profitable year.
Throughout the 2000s, Amazon expanded its original e-commerce bookstore to include hundreds of other products in many other categories, such as software, personal care, music goods, gourmet foods, sporting goods, and photography items like cameras. The expansion of its product range continued over the next few years, with the addition of newer categories like jewelry, baby products and vehicles.
By the middle of the decade, Amazon was thinking beyond e-commerce. In 2005, it launched Amazon Prime, a membership-based service that offers free two-day shipping to Amazon customers in many countries, including the U.S., as well as streaming, shopping and reading benefits. The service has significantly contributed to Amazon's increasing revenue and profits since 2005.
In 2006, Amazon made a successful foray into cloud computing, with the launch of AWS. Supported by an extensive global cloud infrastructure, AWS offers a highly flexible and secure cloud computing environment for organizations in many industries, including automotive, energy, financial services, healthcare, manufacturing, education and government. That same year, Amazon also launched a video-on-demand service known at the time as Unbox.
The company launched the Kindle e-reader in 2007. The same way that amazon.com changed the way people bought books, Kindle reshaped how they read them. This device helps users browse, buy and read e-books, magazines and newspapers from the Kindle Store.
In the late 2000s, Amazon launched the Kindle app for mobile devices (2009) and started Amazon Studios (2010) to develop original movies and TV shows. It also made numerous acquisitions like the audiobook retailer Audible.com (2008) and shoe retailer Zappos.com (2009).
From the 2010s to present day
Amazon debuted its first tablet computer, the Kindle Fire, in 2011 and the Amazon Fire TV Stick, which is part of Amazon's extensive line of streaming media devices, in 2014.
In 2011, the company created a Kindle lending library for Prime members. In 2012, it added a publishing arm with the acquisition of Avalon Books and opened its first Black Friday-deals store in 2013. It also started an online Amazon Art marketplace for fine arts in 2013, which has featured original works by famous artists such as Claude Monet and Norman Rockwell.
In 2014, Amazon launched the Echo smart device embedded with a voice-activated chatbot named Alexa. Alexa was rolled out to consumers in 2015 and was followed by the Alexa-equipped Echo Dot in 2016. In 2025, Alexa powers millions of devices worldwide, as well as many Amazon services like Amazon Prime Video, Amazon Music, and Amazon e-commerce.
Also in 2014, Jeff Bezos bought the Washington Post for $250 million. He continues to own the newspaper as of March 2025. However, several scandals have been associated with his ownership, resulting in staff exits and discontent. These problems have led to significant financial losses for the paper and have eroded its readership base.
Amazon continued its acquisition and product launch spree throughout the decade. In 2017, it forayed into online groceries by acquiring Whole Foods. It also launched Amazon Go, a chain of cashierless grocery stores in 2018.
The rise of in-home shopping during the COVID-19 pandemic of 2020 and 2021 made consumers rely on Amazon's e-commerce platform even more. With an estimated 310 million active users worldwide, it remains a popular choice for online shopping and its popularity is likely to endure in the coming years.
In 2023, Amazon launched Amazon Bedrock, a fully managed service to build and scale generative AI (GenAI) applications. Then, in late 2024, Amazon announced that it would invest $4 billion in AI start-up Anthropic. The strategic collaboration between the two companies aims to enhance Amazon Bedrock's performance, security and privacy capabilities. In the long term, the partnership is expected to strengthen Amazon's GenAI capabilities, particularly in the cloud computing space.

What is AWS?
AWS is a comprehensive and evolving cloud computing platform. Amazon launched the AWS cloud to provide organizations with essential computing services through the internet. By doing so, they could avoid the burden of IT infrastructure management and easily access sophisticated technologies that were previously out of their reach.
The first AWS offerings, Amazon Simple Storage Service (S3) and Amazon Elastic Compute Cloud (EC2) were launched in 2006 (a few months apart from each other) to provide online services for websites and client-side applications. Amazon S3 enables organizations to safely store data while maintaining privacy and control, while Amazon EC2 allows them to access massive amounts of computer processing power without setting up their own expensive data center. Amazon S3 and Amazon EC2 remain the backbone of the company's growing collection of web services.
AWS is one of Amazon's most lucrative businesses, generating segment sales of $28.8 billion in 2024 -- a 19% year-over-year increase from 2023. In 2025, the AWS ecosystem includes more than 200 cloud-based services used by millions of customers worldwide. Some of the most popular AWS services include:
- Amazon Elastic Block Store. EBS is a block-storage service for Amazon EC2.
- Amazon CloudWatch. This service monitors applications and gets insights into the operational health of systems.
- Amazon Relational Database Service. RDS is a service to automate relational database management tasks.
- AWS Lambda. This is a serverless compute service to run code in response to events without having to manage servers or clusters.
- Amazon CloudFormation. This tool provisions infrastructure as code (IaC) to speed up deployment and simplify management.
- Amazon Elastic Load Balancing. ELB is a network service that automatically distributes incoming application traffic to improve network and application scalability.
The AWS ecosystem includes tens of thousands of partners that offer numerous products and services that integrate with AWS to support thousands of use cases. All partners in the Amazon Partner Network (APN) are listed on the AWS Partner Portal. Through this portal, any organization can find an AWS-approved provider to meet its cloud computing needs.
Notable Amazon products and services
Amazon offers an ever-expanding portfolio of services and products. Following is a list of its noteworthy offerings.
Retail
- Amazon Marketplace. Amazon's e-commerce platform enables third-party retailers to showcase and sell their products alongside Amazon items.
- Amazon Fresh. Amazon's grocery pickup and delivery service is currently available in nearly two dozen U.S. cities and a few international locations. A grocery order can be placed through the Amazon Fresh website or the Amazon mobile app. Customers can either get their groceries delivered or visit the store for pickup.
- Amazon Vine. Launched in 2007, Amazon Vine is an invitation-only program in which Amazon selects certain reviewers, sends them certain items free of charge, and invites them to share their experiences using those products. Vine helps manufacturers and publishers get reviews for their products to help shoppers make informed purchases.
- Woot. Founded in 2004 and acquired by Amazon in 2010, Woot offers limited-time offers and special deals on many product categories like clothing, electronics and houseware. Many of these deals rotate daily, and some new deals are offered every 30 minutes.
- Zappos. Amazon bought Zappos in 2009. This online retailer of shoes and clothing carries a wide range of brands, including Nike, Sperry, Adidas and UGG.
- Amazon Merch on Demand. This on-demand printing service enables sellers to create and upload their designs for free. Amazon prints the merchandise -- T-shirts, accessories, etc. -- and delivers them to customers. The creators earn royalties on each sale.
- Amazon Handmade. This platform enables artisans to sell handcrafted products to customers around the world.
Consumer technology
- Amazon Kindle. Kindle is Amazon's first e-reader. It enables users to browse, buy and read e-books, magazines and newspapers from the Kindle Store.
- Amazon Fire tablet. Previously known as Kindle Fire, Amazon's popular Fire tablet competes with Apple's iPad.
- Amazon Fire TV. This line of streaming media players and digital devices delivers streamed video content over the internet to a paired high-definition television. These devices integrate with many streaming services including Amazon's own Prime Video, as well as third-party services like Netflix and Hulu.
- Amazon Fire TV Stick. This compact, plugin streaming device connects to a TV's High-Definition Multimedia Interface, or HDMI, port to display streamed content from various services.
- Amazon Alexa. This cloud-based, AI-powered, voice-controlled personal assistant is designed to answer queries, interact with users, and perform other tasks and commands. Amazon offers tools, application programming interfaces (APIs) and reference solutions to help developers build applications for Alexa.
- Amazon Echo. This is one of Amazon's smart home devices that comes equipped with a speaker. Alexa can listen to a user's voice commands and perform several functions in response, such as providing information about the weather, creating shopping lists and controlling other smart products, such as lights, switches and televisions.
- Amazon Echo Dot. A smaller, puck-shaped version of the original Amazon Echo speaker, an Echo Dot speaker can be placed in any room and can answer questions, play music, and read news and other stories.
- Amazon Echo Show. Part of the Amazon Echo line of speakers, Amazon Echo Show works similarly through Alexa. It also offers a 7-inch touchscreen display to play videos and music and conduct video calls with other Echo users.
- Amazon Astro. This is Amazon's first home monitoring robot that works with Alexa. It allows users to check on the rooms, people or things in their home. The robot can also help with various other household tasks, such as caring for the elderly through notifications and alerts, and following owners from room to room to play TV shows, music or podcasts.
Subscription services
- Amazon Prime. This subscription service provides members access to exclusive shopping and entertainment services, discounts and more. As an example, all Amazon Prime members enjoy free one-day or two-day shipping on qualifying orders.
- Amazon Prime Video. This is Amazon's on-demand video streaming service that offers a selection of thousands of movies and TV shows. The service, included with an Amazon Prime membership, is available in over 200 countries and territories worldwide.
- Amazon Drive. Previously known as Amazon Cloud Drive, Amazon Drive was a cloud storage app that offered limited free and secure online storage for photos, videos and files for Amazon customers. The service was discontinued as of Dec. 31, 2023, and as a result, customers no longer have access to their files on Amazon Drive. However, they can use the Amazon Photos service instead.
- Twitch Prime. Twitch is a video streaming platform that offers a fun and social way to watch people play games, cook, create crafts, and so on. Amazon purchased Twitch in 2014.
- Amazon Prime Music. This is Amazon's music and podcast streaming service. It is free for Prime members.
Digital content
- Amazon Pay. An online transaction processing platform, Amazon Pay enables Amazon account holders to use their Amazon accounts to pay external online merchants, pay bills, book tickets, and buy foods, medicines, insurance, gift cards and gift vouchers.
- Kindle Store. Kindle Store is Amazon's e-commerce store for buying e-books. Accessible from any Kindle device, it uses a recommendation engine to make personalized e-book recommendations to each buyer.
- Amazon Appstore for Android. Amazon's app store for the Android operating system enables users to download games and mobile apps to supported devices. However, on Aug. 20, 2025, Amazon will discontinue this service.
AWS
In addition to the many popular services highlighted previously, the growing AWS universe includes the following products:
- Amazon S3. This is Amazon's scalable, cloud-based object storage service based on a pay-as-you-go model. It provides a scalable way to store any amount of data. In S3, files are known as objects and stored in containers called buckets.
- Amazon Simple Queue Service. Amazon SQS is a fully managed message queuing service for microservices, distributed systems and serverless applications. It uses first-in-first-out (FIFO) queues to ensure that messages sent to systems are always published in the correct order.
- Amazon EC2. Amazon EC2 is Amazon's web-based compute service for workloads. It allows users to access scalable infrastructure on demand. They can also run virtual servers or instances that can be scaled up or down to optimize performance and cost.
- Amazon S3 Glacier storage classes. Amazon S3 Glacier provides storage classes for data archiving. Different classes are available for different access patterns and storage duration.
- AWS Identity and Access Management. AWS IAM enables secure and controlled access to AWS resources and services. It is particularly useful to apply fine-grained permissions, securely scale access across AWS accounts and establish preventive security guardrails on AWS.
- Amazon Redshift. This cloud-based data warehouse service enables users to query petabytes of both structured and semistructured data using standard SQL queries. Redshift analyzes data across data warehouses, operational databases and data lakes, and provides near real-time analytics to support organizational decision-making.
Amazon AI services
- Amazon SageMaker. A fully managed cloud machine learning platform, Amazon SageMaker enables developers and data scientists to build, train and deploy machine learning models. It provides unified access to all data and allows users to use familiar AWS tools for model development, data processing and SQL analytics.
- Amazon Lex. Amazon Lex is an AI chatbot builder. Users can use Lex to build conversational interfaces into any application. It is powered by the same technology as Alexa and uses advanced natural language models to build AI chatbots and voice bots in applications.
- Amazon Polly. This fully managed service allows users to deploy high-quality, natural-sounding human voices in many different languages. It uses deep learning technology to convert any text to an audio stream, including text from articles, web pages and PDF documents.
- Amazon Rekognition. This facial recognition platform uses deep learning to process images and videos and extract information from them. It includes a facial verification feature to detect real users and spoofs. It can also compare faces, extract skewed and distorted text from images and detect unsafe or inappropriate content in images and videos.
- AWS DeepLens. DeepLens was a deep learning-enabled video camera that developers used to build machine learning applications. Amazon ended support for DeepLens on Jan. 31, 2024, and deleted all DeepLens models, projects, and device information from the DeepLens service so users can no longer access it from the AWS console.
- Alexa Voice Service. AVS-powered Alexa built-in devices provided developers with a set of APIs, software development kits, or SDKs, and documentation to add Amazon Alexa's speech and other capabilities to their applications and devices. However, these tools are no longer available. To build devices that connect to Alexa, developers must now sign up for the Works with Alexa (WWA) certification program.
- Amazon Transcribe. This automatic speech recognition (ASR) service automatically converts speech to text. Powered by a next-gen parameter speech foundation model, Transcribe allows developers to add speech-to-text capabilities to their applications.
- Amazon Translate. Amazon Translate can translate large amounts of text from one language to another. It uses machine learning to deliver high-quality translations of user-generated content, online conversations and more.
- Alexa Skills Kit. ASK provides self-service APIs, Skill components, and other tools to build Skills (apps for Alexa).
Amazon privately owned brands
- AmazonBasics. This is Amazon's privately labeled, low-budget brand that mainly sells everyday consumer goods like kitchen, tech, office supplies and household products.
- Mama Bear. This private label of Amazon sells baby wipes, diapers, baby food, vitamins, baby bottles, pacifiers and feeders.
- Presto!. This brand started as a laundry detergent in 2016 but has since added many other household products to its product line. These include paper towels, toilet paper, disinfectants, cleaning liquids and surface cleaning wipes.
- Amazon Essentials. The Amazon Essentials clothing line offers clothes, footwear and accessories for men, women, babies and kids.
- Happy Belly. Introduced in 2016, this is Amazon's private label for food. Its product line includes snacks, teas, coffees, juices and canned fruits.
- Goodthreads. This apparel line offers casual and professional clothes for both men and women.
Notable Amazon subsidiaries and acquisitions
From healthcare to entertainment, Amazon has acquired multiple companies in a variety of sectors over time.
Following is a list of Amazon's notable acquisitions and subsidiary companies:
- IMDb. The world's most popular database for movies, TV, celebrity, video games and streaming online content was acquired by Amazon in 1998.
- Audible. Audible, a book and spoken audio content provider, was acquired by Amazon in 2008 for $300 million.
- Zappos. Amazon acquired this online shoe and clothing retailer in an all-stock deal worth $1.2 billion in 2009.
- Twitch. A social media and video game streaming platform, Twitch was purchased by Amazon for $970 million in 2014.
- Whole Foods. Food, beverage and organic grocery store chain Whole Foods was acquired by Amazon for $13.7 billion in 2017.
- Ring. Amazon took ownership of this home security and smart home company in 2018 for $1 billion.
- Zoox. An autonomous vehicles, robotics and transportation company was acquired as a wholly owned subsidiary by Amazon for $1.2 billion in 2020.
- Metro-Goldwyn-Mayer. Amazon acquired this film and TV studio for $8.5 billion in March 2022.
Amazon controversies and criticisms
Amazon has suffered a massive backlash over the years from multiple sources. The tech giant is also being held responsible for creating the Amazon effect -- the evolution and disruption of the retail market due to the company's monopolistic behaviors.
Following are a few concerns and allegations that Amazon has faced over time:
- Monopolistic and anticompetitive behavior. Due to Amazon's size and economies of scale, it has continuously outpriced local and small shopkeepers in many countries. It is also accused of displacing an open market with a privately controlled one. This is leading to the slow death of the brick-and-mortar store model built.
- Unfair treatment of workers. Amazon is frequently criticized for promoting unfair work conditions in its warehouses, including treating workers as robots, providing low wages and creating unsafe work conditions.
- Huge carbon footprint. Over the past two decades, Amazon has been accused by environmental activists of having a staggering carbon footprint. Transport of any merchandise relies on oil, and since Amazon delivers almost anything to just about everywhere, it leaves a long-lasting carbon footprint.
- E-waste. Amazon is criticized for contributing to the world's e-waste crisis by destroying millions of unused or returned products. This also includes millions of electronics, such as phones, computers and TVs that are toxic to soil, water, air and can potentially harm wildlife, flora and delicate natural ecosystems.
- Counterfeit product listings. Brands, shoppers and lawmakers have scrutinized Amazon because counterfeiters have been listing and selling fake products on Amazon. To crack down on counterfeit products, Amazon destroyed 2 million counterfeit products sent to its warehouses and blocked 10 billion fake listings in 2021. The company has also built tools to identify individual units of enrolled products to ensure that only authentic products reach customers.
- Avoiding taxation. Edging fast toward a monopoly status, Amazon has been criticized for often avoiding tax payments despite making huge profits. According to a report by the Institute on Taxation and Economic Policy, the company avoided around $5.2 billion in corporate federal income taxes in 2021. Many tax authorities have investigated Amazon for tax evasion. Some have let the company off the hook. For example, in December 2023, the EU's top court ruled that Amazon won't have to pay $273 million in back taxes.
Amazon finances
In 30 years, Amazon has grown into a business behemoth with a presence in multiple industries and the revenue to match.
As of the last quarter of 2024, AWS held the largest market share in the cloud infrastructure market. It is trailed by Microsoft Azure and Google Cloud. In addition, it reported revenue of $20 billion in this period, a substantial increase from the $10.6 billion earned in the last quarter of 2023.
In all of 2024, the company's net sales increased to $638.0 billion -- an 11% increase over the 2023 figure of $574.8 billion. Net income also increased to $59.2 billion, compared with $30.4 billion in 2023.
Here are some other notable statistics from a news release published by Amazon on Feb. 6, 2025:
- Net sales. Increased 10% to $187.8 billion in the fourth quarter of 2024, compared with $170 billion in the fourth quarter of 2023.
- Operating income. Increased to $21.2 billion in Q4 2024, compared with $13.2 billion in Q4 2023.
- Net income. In Q4 2024 increased to $20.0 billion, almost twice the number of $10.6 billion in Q4 2023.
- Operating income. Increased from $36.9 billion in 2023 to $68.6 billion in 2024.
- Operating cash flow. Increased by 36% from $84.9 billion in 2023 to $115.9 billion in 2024.
Besides being recognized as a company with business interests in e-commerce, cloud computing and AI services, Amazon also offers an extensive list of subscription services. Learn about these services and the perks they offer.