What is information security management system (ISMS)?
An information security management system (ISMS) is a set of policies and procedures for systematically managing an organization's sensitive data. The goal of an ISMS is to minimize risk and ensure business continuity by proactively limiting the impact of a security breach.
An ISMS typically addresses employee behavior and processes as well as data and technology. It can be targeted toward a particular type of data, such as business continuity, or it can be implemented in a comprehensive way that becomes part of the company's culture. Establishing data security using an ISMS helps prevent, detect and mitigate data breaches, cyberthreats and other cybersecurity risks.
Who needs ISMS?
ISMS, as defined in ISO 27001 and ISO 27002, is scalable and can be used in virtually any kind of organization. Owing to the depth of its content, it is often used to support organizations that already have a cybersecurity defense strategy. By contrast, the National Institute of Standards and Technology's Cybersecurity Framework (CSF) is often considered an effective starting point for building a robust cybersecurity foundation.
By getting certified with ISO 27001, an organization demonstrates its commitment to cybersecurity from risk, operational and audit perspectives. While the certification process can be time-consuming and expensive, it is an integral part of a company's governance, risk and compliance (GRC) activities.
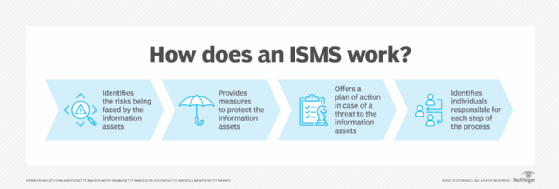
How does ISMS work?
An ISMS provides a systematic approach to managing an organization's information security. Information security encompasses certain broad policies that control and manage security risk levels across an organization.
ISO/IEC 27001 is the international standard for information security and for creating an ISMS. Jointly published by the ISO/IEC, the standard doesn't mandate specific actions but includes suggestions for documentation, internal audits, continual improvement, and corrective and preventive action. To become ISO 27001 certified, an organization requires an ISMS that identifies the organizational assets and provides the following:
- Assessment of the risks the information assets face.
- Steps taken to protect the information assets.
- Plan of action in case a security breach happens.
- Identification of individuals responsible for each step of the information security process.
The goal of an ISMS isn't necessarily to maximize information security, but rather to reach an organization's desired level of information security. These levels of control might vary depending on the specific needs of the industry. For example, since healthcare is a highly regulated field, a healthcare organization might develop a system to ensure sensitive patient data is fully protected.
Benefits of ISMS
ISMS provides a holistic approach to managing the information systems within an organization. This offers numerous benefits, some of which are highlighted below.
- Protects sensitive data. An ISMS protects all types of proprietary information assets whether they're paper-based, preserved digitally or reside in the cloud. These assets can include personal data, intellectual property, financial data, customer data and data entrusted to companies through third parties.
- Meets regulatory compliance. ISMS helps organizations meet all regulatory compliance requirements and contractual obligations and provides a better grasp on legalities surrounding information systems. Since violation of legal regulations comes with hefty fines, having an ISMS can be especially beneficial for highly regulated industries with critical infrastructures, such as finance or healthcare.
- Provides business continuity. When organizations invest in an ISMS, they automatically increase their level of defense against threats. This reduces the number of security incidents, such as cyberattacks, resulting in fewer disruptions and less downtime, which are important factors for maintaining business continuity.
- Reduces costs. An ISMS offers a thorough risk assessment of all assets. This enables organizations to prioritize the highest-risk assets to prevent indiscriminate spending on unneeded defenses and provide a focused approach toward securing them. This structured approach, along with less downtime due to a reduction in security incidents, significantly cuts an organization's total spending.
- Enhances company culture. An ISMS provides an all-inclusive approach to security and asset management throughout the organization that isn't limited to IT security. This encourages all employees to understand the risks tied to information assets and adopt security best practices as part of their daily routines.
- Adapts to emerging threats. Security threats are constantly evolving. An ISMS helps organizations prepare and adapt to newer threats and the continuously changing demands of the security landscape.
ISMS best practices
The ISO 27001 and ISO 27002 standards offer best-practice guidelines for setting up an ISMS. The following is a checklist of best practices to consider before investing in an ISMS:
Obtain senior management support. It is important to enlist senior management support and funding for an ISMS project. Make sure senior management understands how an ISMS will enhance the organization's security posture and its ability to deal with cyberthreats. Keep senior management regularly informed on the project's progress.
Form an ISMS project team. Members of the team should be from the existing cybersecurity department and security operations center (SOC). Consider inviting the chief information security officer and/or chief technology officer to join the project team.
Understand business needs. Before executing an ISMS, it's important for organizations to get a bird's eye view of the business operations, tools and information security management systems to understand the business and security requirements. It also helps to study how the ISO 27001 framework can help with data protection and the individuals who will be responsible for executing the ISMS.
Establish an information security policy. Having an information security policy in place before setting up an ISMS is beneficial, as it can help an organization discover the weak points of the policy. The security policy should typically provide a general overview of the current security controls within an organization.
Monitor data access. Companies must monitor their access control policies to ensure only authorized individuals are gaining access to sensitive information. This monitoring should observe who is accessing the data, when and from where. Besides monitoring data access, companies should also track logins and authentications and keep a record of them for further investigation.
Conduct security awareness training. All employees should receive regular security awareness training. The training should introduce users to the evolving threat landscape, the common data vulnerabilities surrounding information systems, and mitigation and prevention techniques to protect data from being compromised.
Secure devices. Protect all organizational devices from physical damage and tampering by taking security measures to ward off hacking attempts. Tools, such as Google Workspace and Office 365, should be installed on all devices, as they offer built-in device security.
Encrypt data. Encryption prevents unauthorized access and is the best form of defense against security threats. All organizational data should be encrypted before setting up an ISMS, as it will prevent any unauthorized attempts to sabotage critical data.
Back up data. Backups play a key role in preventing data loss and should be a part of a company's security policy before setting up an ISMS. Besides regular backups, the location and frequency of the backups should be planned out. Organizations should also design a plan to keep the backups secure, which should apply to both on-premises and cloud backups.
Conduct an internal security audit. An internal security audit should be conducted before executing an ISMS. Internal audits are a great way for organizations to gain visibility over their security systems, software and devices, as they can identify and fix security loopholes before executing an ISMS.
ISMS implementation
There are various ways to set up an ISMS. Most organizations either follow a plan-do-check-act process or study the ISO 27001 international security standard which effectively details the requirements for an ISMS.
The following steps illustrate how an ISMS should be implemented:
- Define the scope and objectives. Determine which assets need protection and the reasons behind protecting them. Consider the preference of what the clients, stakeholders and trustees want to be protected. Company senior management should also define clear-cut security objectives for the areas of application and limitations of the ISMS. If the organization has a SOC, it should be responsible for deploying the ISMS.
- Identify assets. Identify the assets that are going to be protected. This can be achieved by creating an inventory of business-critical assets including hardware, software, services, information, databases and physical locations by using a business process map.
- Recognize the risks. Once the assets are identified, risk management and security practices specify performing a risk assessment in which risk factors are analyzed and scored by assessing the legal and regulatory requirements, and compliance guidelines. Organizations should also weigh the effects of the identified risks. For example, they could question the level of impact a breach of information assets' confidentiality, availability or integrity would create, or the probability of that breach's occurrence. The end goal should be to arrive at a conclusion outlining which risks are acceptable and which must be tackled at all costs due to the potential amount of harm involved.
- Identify mitigation measures. An effective ISMS not only identifies risk factors but also provides satisfactory measures to effectively mitigate and combat them. The mitigation measures should lay out a clear treatment plan to avoid the risk altogether. This includes an effective incident management plan. For example, a company trying to avoid the risk of losing a laptop with sensitive customer data should prevent that data from being stored on that laptop in the first place. An effective mitigation measure would be to set up a policy or rule that doesn't permit employees to store customer data on their laptops.
- Write ISMS documentation. This step gathers all knowledge generated from the previous steps and converts it to specific procedures and policies in support of the ISMS. Be sure to review guidance in ISO 27002 when preparing documentation. Written policies and procedures are important audit evidence.
- Implement the ISMS. Once the policies and procedures have been completed and approved, deploy and test the actions needed to achieve the objectives spelled out in the ISMS.
- Make improvements. All the previous measures and security metrics should be monitored, audited and checked regularly for effectiveness and compliance. If the monitoring reveals any deficiencies or new risk management factors, then restart the ISMS process from scratch or make modifications as needed. This enables the ISMS to rapidly adapt to changing conditions and offers an effective approach to mitigating the information security risks for an organization. Establish a schedule of ISMS assessments and audits, along with a process for continuous improvement.
A number of IT security frameworks and cybersecurity standards exist to help organizations protect company. Learn about the top IT security frameworks and standards. Also, check out this enterprise cybersecurity hygiene checklist.